🌟 Cybersecurity Weekly Insights: Unfolding the Digital Landscape! 🌟
✅Weekly general new public vulnerabilities report! 🔥
🚀 Introduction
Hello, cyber enthusiasts! 🌐 Welcome to another thrilling edition of our weekly cybersecurity newsletter, where we decode the digital world's latest happenings. This week, we've seen a fascinating mix of vulnerabilities, trends, and insights that emphasize the ever-evolving nature of our digital environment. From intriguing comparisons between vulnerability trends to spotlighting the companies facing the most challenges, our newsletter will take you on a journey through the latest in cybersecurity. Let's dive into the depths of digital defense and discover the patterns that shape our online safety!
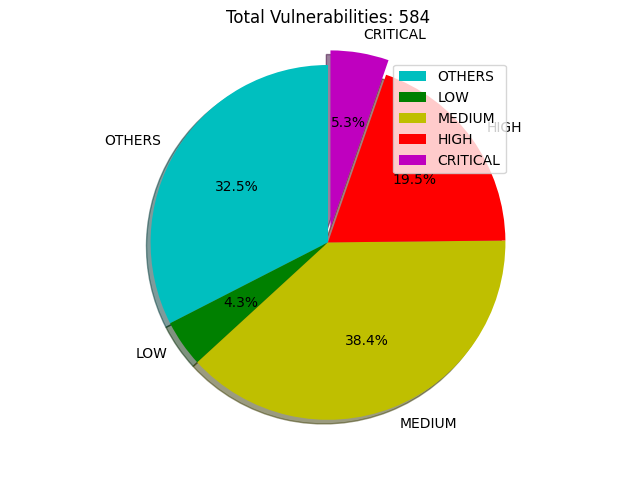
📊 1. This Week's Vulnerability Roundup
This week has been bustling with cybersecurity activity! We've encountered:
190 OTHERS Vulnerabilities
25 LOW Vulnerabilities
224 MEDIUM Vulnerabilities
114 HIGH Vulnerabilities
31 CRITICAL Vulnerabilities
🔍 Conclusion: The substantial number of MEDIUM and HIGH vulnerabilities underscores the persistent need for vigilance and robust security measures. It's crucial to stay updated and proactive in addressing these vulnerabilities to safeguard our digital realms.
📈 2. Vulnerability Comparison: This Week vs. Last Week
Let's compare the current week's data with the last:
OTHERS: 20 previously, 190 now
LOW: 16 previously, 25 now
MEDIUM: 317 previously, 224 now
HIGH: 348 previously, 114 now
CRITICAL: 178 previously, 31 now
🔍 Conclusion: There's a noticeable decrease in MEDIUM, HIGH, and CRITICAL vulnerabilities, which is a positive sign. However, the increase in LOW and OTHERS categories suggests emerging areas that require our attention.
📌 3. Vulnerabilities Classified by Status
Our analysis shows:
17 Received
318 Awaiting Analysis
70 Undergoing Analysis
166 Analyzed
0 Modified, Deferred, or Rejected
🔍 Conclusion: The majority of vulnerabilities are 'Awaiting Analysis,' indicating a backlog and the need for more resources in the analysis phase to expedite the response to potential threats.
🏆 4. Top 10 Companies Reporting Vulnerabilities
Here's the leaderboard for this week:
Mitre: 88 Vulnerabilities
Wpscan: 57 Vulnerabilities
Vuldb: 47 Vulnerabilities
Oracle: 43 Vulnerabilities
Github: 34 Vulnerabilities
Skyworthdigital: 25 Vulnerabilities
Huawei: 22 Vulnerabilities
Redhat: 18 Vulnerabilities
Patchstack: 17 Vulnerabilities
Google: 15 Vulnerabilities
🔍 Conclusion: The diverse range of companies on this list shows that vulnerabilities are a universal challenge, cutting across various sectors and sizes of organizations.
⚠️ 5. Top 10 Critical Vulnerabilities
1. CVE-2023-22527: CRITICAL:10.0
Description: A template injection vulnerability in older versions of Confluence Data Center and Server.
Solution: Update to the latest version of Confluence Data Center and Server. The most recent versions are not affected by this vulnerability.
2. CVE-2021-4434: CRITICAL:10.0
Description: The Social Warfare plugin for WordPress, vulnerable to RCE via the 'swp_url' parameter.
Solution: Update to a version later than 3.5.2 of the Social Warfare plugin to mitigate this vulnerability.
3. CVE-2024-0643: CRITICAL:10.0
Description: Unrestricted file upload in C21 Live Encoder and Live Mosaic product, version 5.3.
Solution: Restrict and validate file uploads on the server side, and update the C21 Live Encoder and Live Mosaic to the latest version with security patches.
4. CVE-2023-34063: CRITICAL:9.9
Description: Missing Access Control vulnerability in Aria Automation.
Solution: Implement strict access controls and update Aria Automation to the latest version with this vulnerability patched.
5. CVE-2023-50729: CRITICAL:9.8
Description: Unrestricted file upload vulnerability in Traccar GPS tracking system prior to version 5.11.
Solution: Upgrade to Traccar version 5.11 or later, which addresses this vulnerability.
6. CVE-2023-6049: CRITICAL:9.8
Description: PHP Object Injection in Estatik Real Estate Plugin for WordPress before 4.1.1.
Solution: Update the Estatik Real Estate Plugin to version 4.1.1 or later to patch this vulnerability.
7. CVE-2023-6623: CRITICAL:9.8
Description: Local File Inclusion attacks in Essential Blocks WordPress plugin before 4.4.3.
Solution: Update the Essential Blocks plugin to version 4.4.3 or newer to secure against this attack.
8. CVE-2023-52103: CRITICAL:9.8
Description: Buffer overflow vulnerability in the FLP module.
Solution: Apply patches and updates provided by the software vendor to mitigate this vulnerability.
9. CVE-2024-0571: CRITICAL:9.8
Description: Stack-based buffer overflow in Totolink LR1200GB firmware.
Solution: Update the Totolink LR1200GB firmware to a version that addresses this vulnerability. Contact the vendor for the latest updates.
10. CVE-2024-0572: CRITICAL:9.8
Description: Critical buffer overflow in Totolink LR1200GB firmware.
Solution: Similar to CVE-2024-0571, ensure your Totolink LR1200GB firmware is updated to the latest version with security fixes.
🔍 Conclusion: The high severity scores of these vulnerabilities highlight the critical need for immediate action and patch management.
🚨6. Public Exploits Update: Confluence RCE Vulnerability
In our ongoing commitment to keep you informed about the latest cybersecurity threats and developments, we bring you an important update regarding a public exploit:
CVE-2023-22527: Confluence RCE Vulnerability
Repository: CVE-2023-22527_Confluence_RCE
Description: This repository contains a Proof of Concept (PoC) for the CVE-2023-22527 vulnerability. It specifically targets the Remote Code Execution (RCE) vulnerability found in Confluence Data Center and Confluence Server. The exploit allows an attacker to execute arbitrary code remotely, posing a significant security risk.
🛡️ What This Means for You: The availability of this PoC in the public domain elevates the risk associated with CVE-2023-22527. Organizations using Confluence Data Center and Server must urgently assess their exposure to this vulnerability and take immediate steps to mitigate the risk.
Immediate Action Steps:
Assess Your Systems: Determine if your organization is running a vulnerable version of Confluence Data Center or Server.
Apply Updates: If affected, promptly update to the latest, non-vulnerable version of the software.
Monitor for Suspicious Activity: Keep an eye on your systems for any signs of compromise or unusual activity.
Review Security Posture: Reevaluate your cybersecurity measures to prevent future vulnerabilities.
🧠 7. Pattern Analysis and Conclusion
After analyzing this week's data, a few key patterns emerge:
Shift in Vulnerability Severity: A decline in MEDIUM, HIGH, and CRITICAL vulnerabilities is encouraging, but the rise in LOW and OTHERS categories suggests new areas of potential risk.
Analysis Backlog: The high number of vulnerabilities 'Awaiting Analysis' indicates a bottleneck in the vulnerability management process.
Diversity in Affected Companies: Vulnerabilities are not limited to a specific sector or size, emphasizing the universal nature of cybersecurity challenges.
🌟 To our non-technical audience: While the landscape of cybersecurity is complex, this week's trends show a dynamic shift towards addressing and managing digital threats. It's a continuous journey of adaptation, vigilance, and proactive measures to stay ahead of potential risks. Let's embrace cybersecurity as an integral part of our digital lives! 💻🔒
Stay Safe and Informed! Your Cybersecurity Weekly Team 😊🔐