Cybersecurity Spotlight: This Week's Vulnerability Digest 🛡️✨
✅Weekly general new public vulnerabilities report! 🔥
Introduction
Welcome to this week’s edition of our cybersecurity newsletter! 🚀 In our latest roundup, we’re diving deep into the heart of digital defense, highlighting the critical vulnerabilities that have surfaced, comparing trends with previous weeks, and giving you the insights you need to stay secure. From the ever-evolving landscape of threats to the top companies grappling with vulnerabilities, we’ve got your back. Let’s embark on this enlightening journey through the cyber wilderness, armed with knowledge and the power to protect. 🛡️💡
All the information provided in this post has been extracted from the National Vulnerability Database (NVD) from National Institute of Standards and Technologies (NIST) from the government of US.
1. Weekly Vulnerability Roundup
This week, our vigilant eyes caught a spectrum of vulnerabilities shaking the digital realm:
143 OTHERS
20 LOW
263 MEDIUM
122 HIGH
57 CRITICAL
Conclusion: The diversity and volume of threats continue to remind us of the persistent vigilance needed in our cyber practices. Particularly, the presence of 57 critical vulnerabilities underscores the importance of immediate action and updates. 🚨
2. Vulnerability Comparisons: This Week vs. Last Week
Reflecting on the past to secure our future, here’s how the numbers stack up:
Others: From 89 to 143 📈
Low: From 41 to 20 📉
Medium: From 218 to 263 📈
High: From 135 to 122 📉
Critical: From 50 to 57 📈
Conclusion: The fluctuations highlight an evolving threat landscape. The increase in 'Others' and 'Critical' categories signals a need for heightened alertness and robust defensive strategies. 🔍🔐
3. Vulnerability Status Classification
Vulnerabilities by status paint a detailed picture of the cybersecurity workflow:
50 Received
315 Awaiting Analysis
93 Undergoing Analysis
142 Analyzed
0 Modified
0 Deferred
5 Rejected
Conclusion: The bulk of vulnerabilities awaiting and undergoing analysis signifies a proactive approach towards identification and mitigation, but also underscores the challenges of keeping pace with emerging threats. 🧐
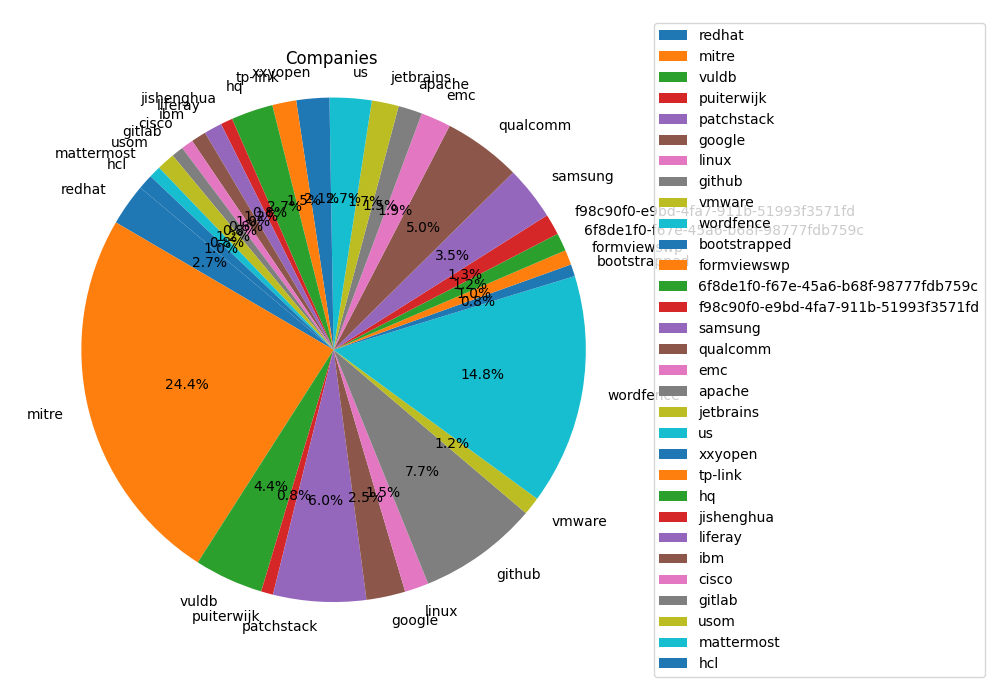
4. Top 10 Reporting Companies
The frontline defenders, reporting the most vulnerabilities:
Mitre: 127 vulnerabilities
Wordfence: 77 vulnerabilities
GitHub: 40 vulnerabilities
Patchstack: 31 vulnerabilities
Qualcomm: 26 vulnerabilities
VulDB: 23 vulnerabilities
Samsung: 18 vulnerabilities
RedHat: 14 vulnerabilities
US: 14 vulnerabilities
HQ: 14 vulnerabilities
Conclusion: The wide array of companies, from tech giants to security specialists, reporting vulnerabilities showcases the collaborative effort in fortifying the digital ecosystem. 🌐💪
5. Vulnerabilities by Category
A closer look at the nature of vulnerabilities:
12 RCE
54 SQL Injection
95 XSS
0 Insecure Deserialization
0 Misconfiguration
Conclusion: The predominance of XSS and SQL Injection vulnerabilities highlights the critical need for secure coding practices and the implementation of stringent input validation measures. 🛠️🔒
6. Vulnerabilities in Famous Companies
Notable companies on the radar:
Google: 3 vulnerabilities
Cisco: 3 vulnerabilities
IBM: 19 vulnerabilities
Meta: 1 vulnerability
Intel: 3 vulnerabilities
Conclusion: Even the giants are not immune. Continuous vigilance and updates are paramount for all, irrespective of size or reputation. 🏢🔧
7. Top 10 Critical Vulnerabilities
The most severe vulnerabilities demanding immediate attention, along with solutions for end-users:
CVE-2024-24594: CRITICAL:9.9
Description: A cross-site scripting (XSS) vulnerability in all versions of the web server component of Allegro AI’s ClearML platform allows a remote attacker to execute a JavaScript payload when a user views the Debug Samples tab in the web UI.
Solution: Users should be vigilant about any updates provided by Allegro AI to address this vulnerability. Regularly monitoring the official Allegro AI or ClearML resources for security advisories and applying updates as soon as they are available is recommended.
CVE-2024-24830: CRITICAL:9.9
Description: OpenObserve's "/api/{org_id}/users" endpoint vulnerability allows authenticated users to elevate privileges improperly.
Solution: Upgrade to OpenObserve release version 0.8.0 or later where this vulnerability is fixed. Users should apply the update immediately to mitigate unauthorized privilege escalation.
CVE-2024-20011: CRITICAL:9.8
Description: In alac decoder, a possible information disclosure due to an incorrect bounds check could lead to remote code execution with no additional execution privileges needed.
Solution: Patch ID: ALPS08441146. Users should apply the update provided by their device manufacturer as soon as it becomes available to address this vulnerability.
CVE-2021-4436: CRITICAL:9.8
Description: The 3DPrint Lite WordPress plugin before 1.9.1.5 allows unauthenticated users to upload arbitrary files to the web server.
Solution: Users are advised to update to version 1.9.1.5 or later of the 3DPrint Lite plugin where this vulnerability has been fixed.
CVE-2024-23108: CRITICAL:9.8
Description: Fortinet FortiSIEM versions 7.1.0 through 7.1.1 and others contain an os command injection vulnerability.
Solution: Fortinet has addressed this vulnerability in recent releases. Users should immediately upgrade their FortiSIEM to a patched version as advised by Fortinet.
CVE-2024-23109: CRITICAL:9.8
Similar to CVE-2024-23108, this vulnerability in Fortinet FortiSIEM allows os command injection. The solution is the same: upgrade to a version where this vulnerability is addressed.
CVE-2024-0323: CRITICAL:9.8
Description: Use of a Broken or Risky Cryptographic Algorithm vulnerability in B&R Industrial Automation Automation Runtime.
Solution: Affected users should update Automation Runtime to version 14.93 or later, where this vulnerability has been mitigated.
CVE-2023-6933: CRITICAL:9.8
Description: The Better Search Replace plugin for WordPress is vulnerable to PHP Object Injection up to version 1.4.4.
Solution: Users should update to a version later than 1.4.4 to mitigate the risk of PHP Object Injection attacks.
CVE-2023-6989: CRITICAL:9.8
Description: The Shield Security plugin for WordPress is vulnerable to Local File Inclusion up to version 18.5.9.
Solution: Users should update to a version later than 18.5.9 to prevent unauthorized execution of PHP files on the server.
CVE-2024-0709: CRITICAL:9.8
Description: The Cryptocurrency Widgets – Price Ticker & Coins List plugin for WordPress is vulnerable to SQL Injection from versions 2.0 to 2.6.5.
Solution: Users are advised to update to a version later than 2.6.5 where this SQL Injection vulnerability is addressed.
Conclusion: These critical vulnerabilities underscore the imperative for organizations and end-users to apply updates and patches diligently. Keeping software up to date is one of the most effective defenses against the exploitation of known vulnerabilities. Stay informed, stay secure, and ensure your digital assets are protected with the latest security measures. 🛡️🔒
8. Public Exploits for Top Vulnerabilities
In our commitment to keeping you informed and secure, we delve into the publicly available exploits for the vulnerabilities highlighted in our report. Currently, we have detailed information on a public exploit for one of the critical vulnerabilities listed:
CVE-2023-6933 Public Exploit Details
For CVE-2023-6933, related to the Better Search Replace plugin for WordPress, a public exploit has been identified and detailed information is available online. The exploit demonstrates how attackers could leverage the PHP Object Injection vulnerability to potentially cause harm.
Repository: CVE-2023-6933
Description: The GitHub repository provides an introduction to the CVE-2023-6933 vulnerability, illustrating the potential for unauthenticated attackers to exploit the PHP Object Injection flaw in the Better Search Replace plugin for WordPress. While the repository does not provide a step-by-step exploit code, it offers valuable insights into the nature of the vulnerability and underscores the importance of applying security updates promptly.
Conclusion: The availability of public exploit details for CVE-2023-6933 serves as a crucial reminder of the ever-present threat posed by vulnerabilities in widely used plugins and software. It emphasizes the necessity for web administrators and users to stay vigilant, regularly monitor their systems for updates, and apply patches as soon as they become available to mitigate the risks associated with such vulnerabilities.
Pattern Analysis and Conclusion
This week’s analysis reveals an uptick in 'Others' and 'Critical' vulnerabilities, underscoring a dynamic and challenging cybersecurity landscape. The proactive identification and reporting from a diverse set of companies are commendable, yet the increased numbers reflect the relentless efforts required to safeguard our digital domains. The concentration of XSS and SQL Injection vulnerabilities reiterates the importance of foundational security practices in development.
Our journey through this week’s vulnerabilities underscores a universal truth in the realm of cybersecurity: vigilance, collaboration, and education are our best defenses against the tides of threats. Let’s carry forward the torch of awareness, update diligently, and champion secure practices in our digital communities. Together, we can forge a safer cyber future. 🔐💡🚀
Stay secure and enlightened until our next dispatch! 🌟